Intro
AWS has unveiled its official Prescriptive Guidance for AWS Cloud Security Maturity [1]. This resource is aimed at assisting Chief Security Officers (CSOs) and Architects in crafting their cloud security strategies and evaluating their progress against a maturity model.
This blog post provides a suggestion on how to distribute the AWS Services over suggested AWS Foundation Core Accounts and how to manage the AWS Resources with Terraform [2] provisioned through granular CI/CD Pipelines.
Reference Implementation
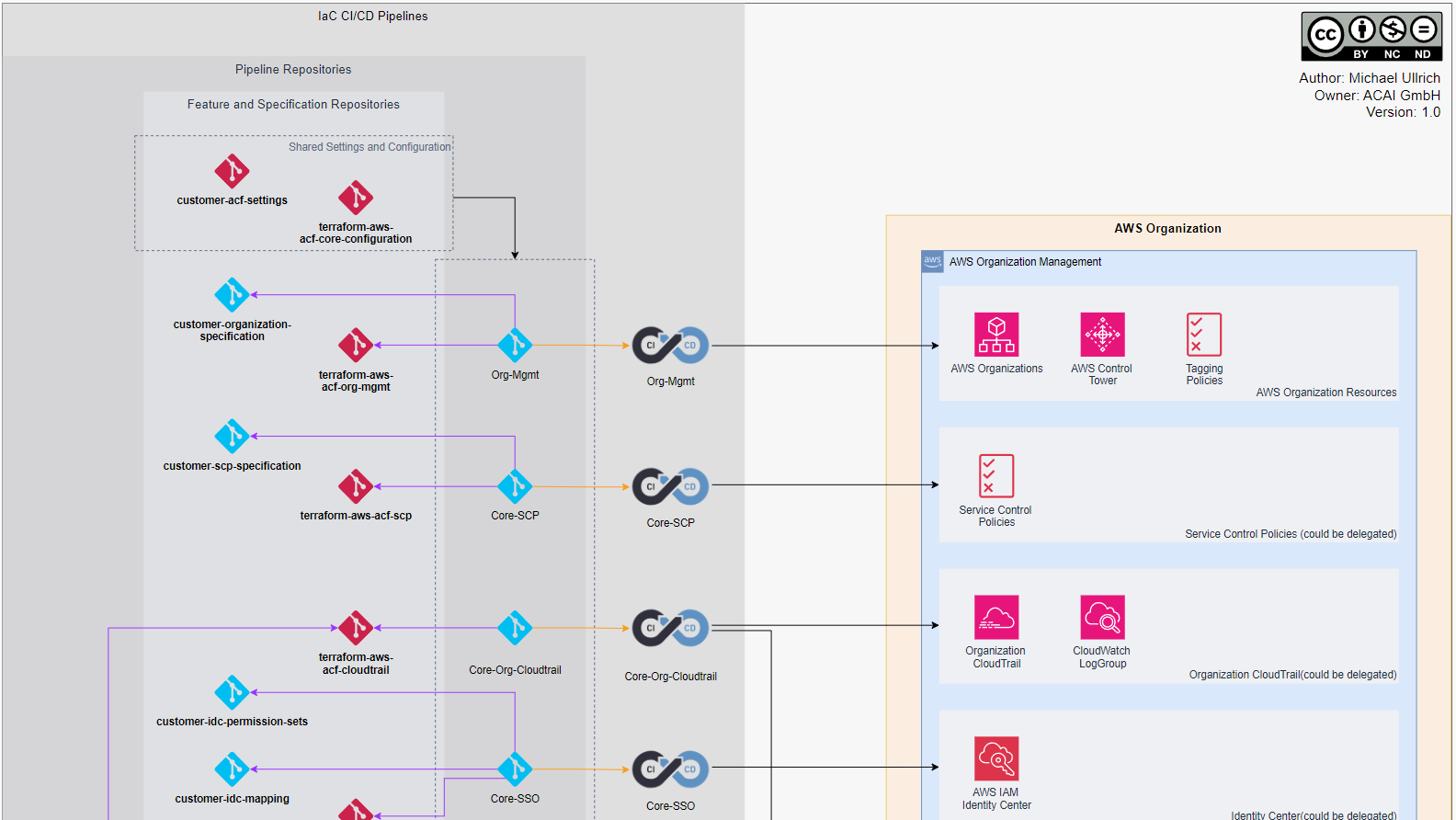
The following diagram illustrates an Infrastructure as Code (IaC) Continuous Integration and Deployment (CI/CD) pipeline to maintain the Foundation Core assets AWS Organization.
The diagram contains repositories (for pipelines, features and specifications), AWS accounts and their AWS services and highlights the interconnectivity between repos and CI/CD pipelines. Most of the feature repositories are part of the ACAI Cloud Foundation (ACF).

All Foundation Core pipelines leverage the following ACF repos for sharing static and dynamic information:
| Repository | Description |
|---|---|
| customer-acf-settings | A hierarchical HCL-map organized according to the Foundation Capability domains, which include governance, security, and connectivity, along with their specific features. |
| acf-core-configuration | Storing and distribution of dynamic information (e.g. KMS-Key ID). |
The following table outlines the Foundation Core pipelines :
| Pipeline | Used ACF Module(s) | Description | Target Accounts | AWS Services in scope |
|---|---|---|---|---|
| Org-Mgmt | acf-org-ou-mgmt, acf-org-delegation | OU-Hierarchy, service delegation, tagging policies | AWS Org Management | AWS Organizations, AWS Control Tower (optional) |
| Core-Account-Lifecycle | acf-account-lifecycle | Account vending, tagging, OU placement, decomissioning | AWS Org Management | AWS Organizations |
| Core-SCP | acf-scp | Specification and assignment of Service Control Policies | AWS Org Management | AWS Organizations |
| Core-Org-CloudTrail | acf-org-cloudtrail | Configuration of the Organization CloudTrail | AWS Org Management or delegated admin, Core Log Archive | AWS CloudTrail, Amazon CloudWatch, Amazon S3, AWS KMS |
| Core-SSO | acd-idc | Definition of Permission Sets and management of the assignments | AWS Org Management or delegated admin | AWS IAM Identity Center |
| Core-Security | acf-firewall-manager | Heart of Security Operations | Core Security | AWS Security Hub, Amazon GuardDuty, Amazon Detective, AWS Config, AWS Firewall Manager, AWS Lambda |
| Core-Security-SEMPER | acai-semper | ACAI solution for security finding lifecycle management | Core Security, Core Log Archive | AWS Lambda, Amazon S3, AWS KMS |
| Core-Logging | acf-logging | Blackhole for audit-logs | Core Log Archive | Amazon S3, AWS KMS, Amazon SNS |
| Core-Image-Factory | acf-image-factory | Lifecycle management for golden images | Core Image Factory | Lambda, EC2 Image Builder, ECR, Amazon Inspector |
| Core-Private-CA | acf-private-ca | Private CA | Core Private CA | AWS Private CA |
| Core-Backup | acf-backup | Backup vault and policies | Core Central Backup | AWS Backup |
| Core-Networking | acf-networking | All networking related aspects | Core Networking | Amazon VPC, AWS Certificate Manager, AWS Resource Access Manager, Amazon Route 53, Amazon Cloudfront, AWS WAS, AWS Network Firewall |
| Core-Baselining | acai-provisio | Individually baseline all accounts of the AWS Organization | Core Baselining | AWS Step Functions, AWS CodeBuild |
ACAI Consulting is specialized in AWS Multi Account Security and Governance. If you have any questions, feel free to get in touch with us: blog@acai.gmbh